A Modified Gresham's Law of Stablecoins
“The one thing that’s missing, but that will soon be developed, is a reliable e-cash, a method whereby on the Internet you can transfer funds from A to B without A knowing B or B knowing A. […] Of course, it has its negative side. It means that gangsters, the people who are engaged in illegal transactions, will also have an easier way to carry on their business.” Milton Friedman, Interview at University of California at Berkeley, 1999, cited by Steve Hanke, “Friedman and Hanke on Bitcoin,” February 20, 2014.
The history of payments is an arms race that pits law enforcement against criminals, with criminals typically maintaining an edge. Paper currency, wire transfers, shell companies, offshore banking, prepaid cards — each opened a channel for illicit finance, drawing imperfect and incomplete legal and regulatory reactions. Criminals adapt to financial innovations, the payments police react, and a gap for illicit activity lingers when the next innovation arrives.
The newest technology is crypto and stablecoins. Milton Friedman saw them coming. Nearly a decade before Bitcoin launched, he described the technology that stablecoins have become: e-cash that is a digital peer-to-peer bearer instrument. He knew gangsters would make it their own, and they have.
Friedman's observation has a counterpart in an older principle about money. Gresham's Law — an observation associated with the Elizabethan financier Sir Thomas Gresham and later formalized by economists — holds that “bad money” drives out “good money.” When two currencies circulate at the same legal value despite differences in intrinsic value, holders spend the cheaper coins and hoard the more valuable ones. In the era of metallic coinage, the rule was simple: spend the lighter coin, keep the heavier.
In this post, we argue that a modified version of Gresham’s Law applies to stablecoins. Stablecoins are private digital tokens that promise to maintain a fixed value — typically one U.S. dollar each — backed by reserve assets whose composition varies by issuer. The two largest are Tether’s USDT and Circle’s USDC. Their dollar peg might appear to make them interchangeable, but it does not. Users who value anonymity gravitate toward what Gresham might have called the bad money: the coin with weaker oversight that makes identification easier to avoid. Put differently: in stablecoins, as in metallic coinage, bad money drives out good — where “bad” means less transparent and less certain in value.
The quality gap between the two biggest issuers of U.S.-dollar stablecoins is unmistakable. Tether's USDT is less well-backed: roughly 80 percent of its reserves are in cash and U.S. Treasuries, but the remainder includes gold, bitcoin, and secured loans. While BDO publishes quarterly attestations of these holdings, Tether has never completed a full audit by a Big Four accounting firm. By contrast, more than 85 percent of USDC's reserves sit in the BlackRock Circle Reserve Fund, a money market fund that holds exclusively U.S. Treasury securities and overnight Treasury repos. Circle publishes weekly disclosures of USDC's reserve holdings, and Deloitte audits Circle annually. As a licensed money transmitter, Circle also has been subject for more than a decade to the regulatory jurisdiction of the New York Department of Financial Services, which insists on strict standards for stablecoins. Tether is not an NYDFS-licensed entity: in 2021 the New York Attorney General required that it cease trading with New York residents.
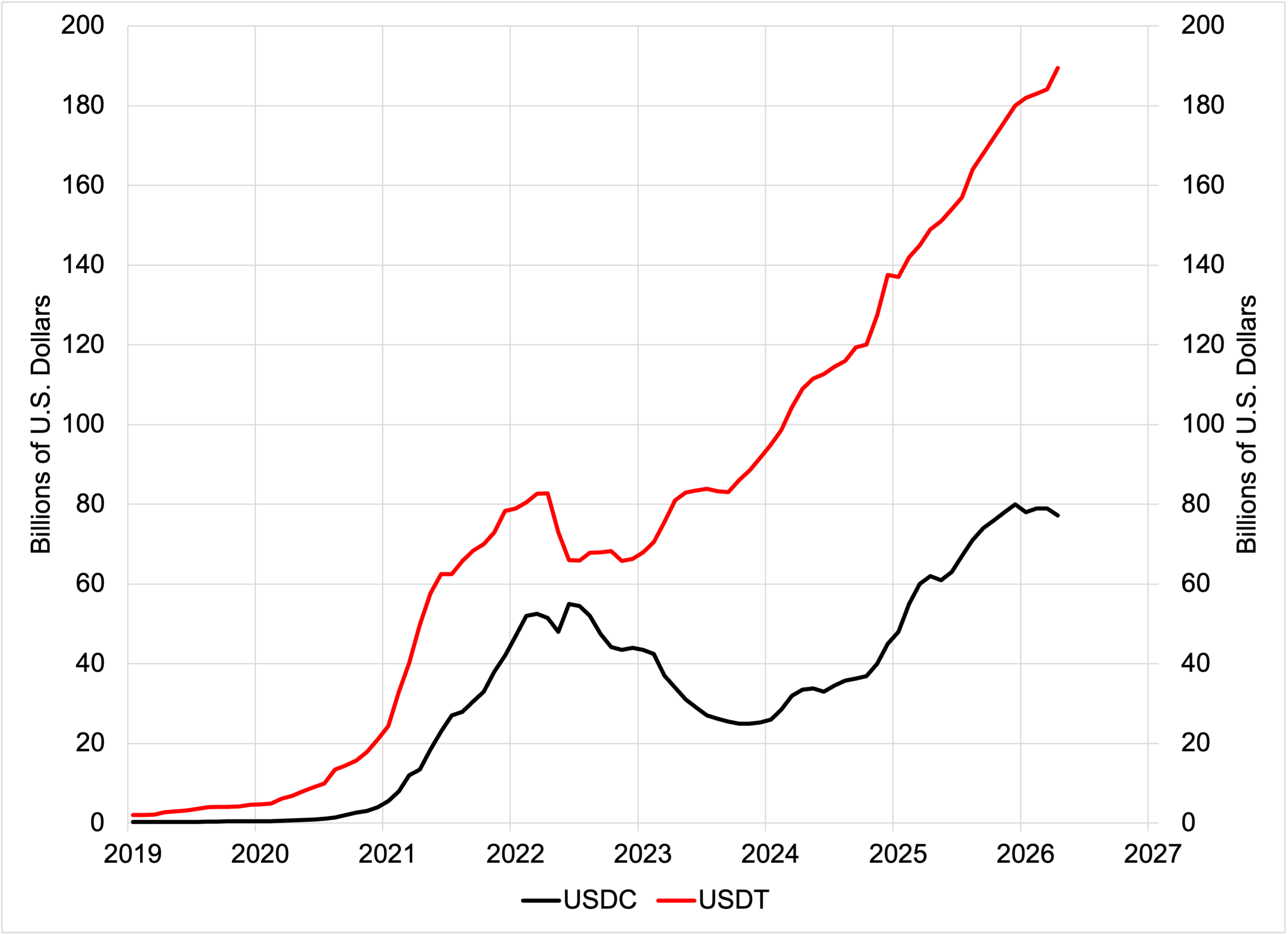
Nevertheless, the global market has opted for the less-regulated and less-transparent coin. USDT circulation sits at roughly $189 billion, USDC at roughly $77 billion. And, as we see in Figure 1, the gap is widening. As we discuss below, a network externality reinforces this gap: the more users a stablecoin attracts, the more useful it becomes.
Figure 1. Market Capitalization: USDT and USDC (monthly, end-of-month, billions of U.S. dollars), 2019–2026
Sources: CoinGecko, CoinMarketCap, DefiLlama.
The Modified Gresham’s Law in Action
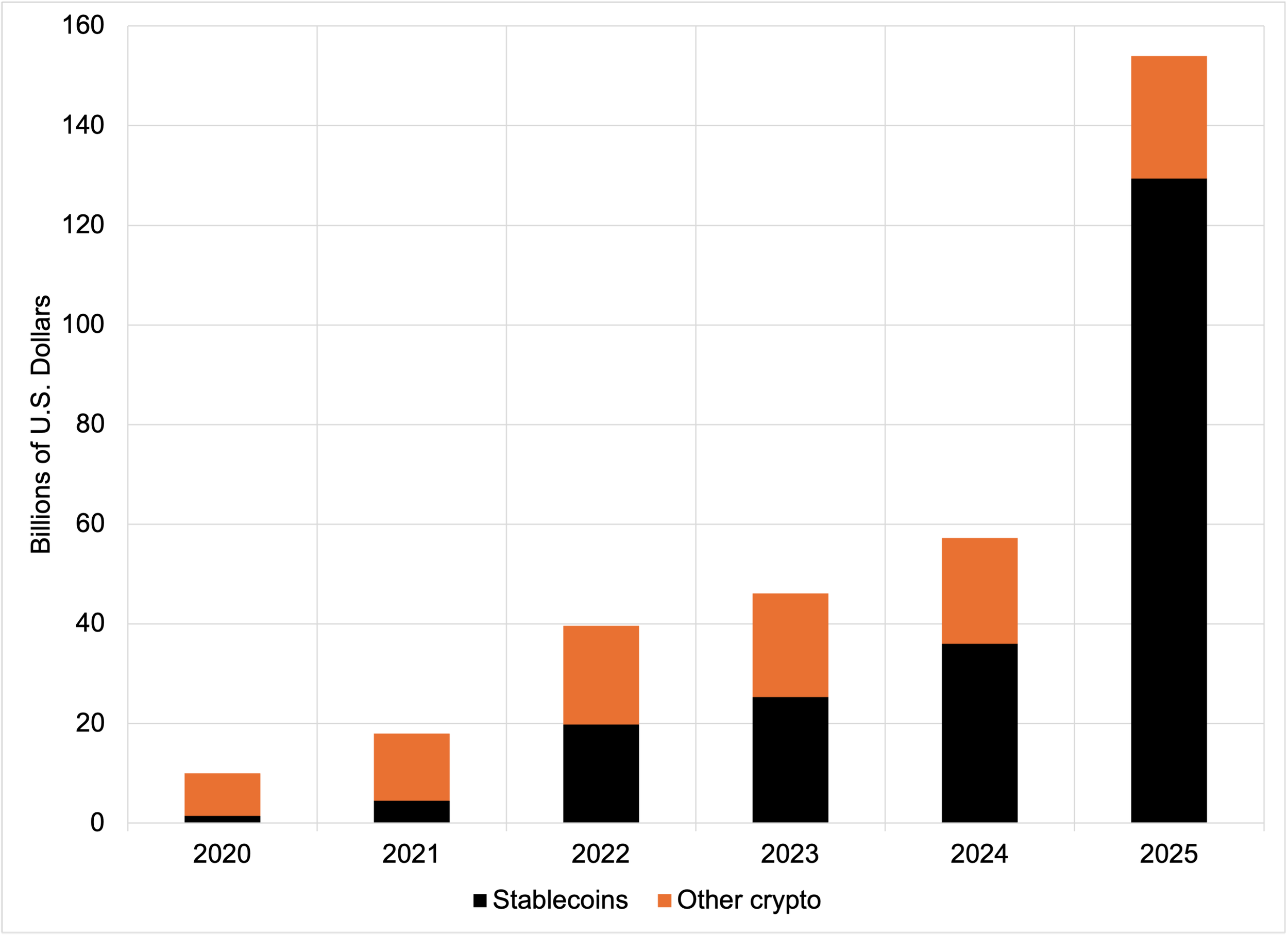
Three pieces of evidence connect this Gresham’s Law gap to demand for anonymity and suggest it will persist. First, crypto use for criminal purposes has risen sharply. For example, the Chainalysis 2026 Crypto Crime Report estimates that illicit blockchain addresses received at least $154 billion in cryptocurrency in 2025 — a more than 15-fold increase from roughly $10 billion in 2020. Second, Figure 2 traces a striking reversal: stablecoins accounted for only a small fraction of illicit transaction volume in 2020 but surpassed Bitcoin to become the leading vehicle for money launderers and sanctions evaders by 2024–2025. More broadly, stablecoin transaction volume in the first quarter of 2026 reached a record 75% of all crypto trading (see here).
Figure 2. Illicit cryptocurrency transaction volume by asset type (Billions of U.S. Dollars), 2020–2025
Source: Chainalysis Crypto Crime Report, various years. Stablecoin shares are published for 2020, 2024, and 2025; shares for 2021–2023 are estimated from Chainalysis published charts.
Third, as we will see in the next section, the anti-money-laundering rules for domestic institutions — banks, exchanges, custodians, and stablecoin issuers — do not extend to bearer instruments held and traded abroad. It is no wonder, then, that Tether issues USDT — the exemplar of the modified Gresham’s Law in action — under the less rigorous regulatory regime in El Salvador.
We now turn to what the current global stablecoin framework allows: how criminals retain anonymity, what stablecoin issuers can and cannot see, and where the issuers' enforcement powers run out.
The Bank Secrecy Act Reaches Institutions, Not Instruments
Following numerous revisions and enhancements since its enactment in 1970, the Bank Secrecy Act (BSA) imposes specific responsibilities on institutions: they must identify customers (including foreign accounts), monitor transactions, file suspicious activity reports, and share information with the U.S. Government regarding the financing of terrorism (see here). Domestic stablecoin issuers, exchanges and custodians now face comparable obligations under the 2025 GENIUS Act.
However, the rules do not reach the instruments themselves. This distinction is critical. Consider the difference between a custodial account and a self-hosted wallet. A user who buys USDC on the Coinbase exchange in the United States does not hold the tokens in a wallet — Coinbase does. The user holds a claim against Coinbase, the custodian. Coinbase knows exactly who its customers are, and the BSA and GENIUS Act apply in full.
Shifting those tokens to a self-hosted wallet — say, using software like MetaMask or a hardware device — changes everything. The user now holds the tokens directly and accesses them with a private cryptographic key. The blockchain address that holds them is not associated with any name. That change in technology fundamentally alters the tokens’ economic character. They become the digital equivalent of a briefcase of cash — bearer instruments. The holder of the cryptographic key owns the claim. Like a briefcase, it can be handed to anyone, anywhere, without having to ask a bank. It can cross a border without obtaining a visa or even showing a passport.
Cash transfers are completely anonymous: neither payer nor recipient need know the other’s identity. Similarly, the issuer of a stablecoin can only observe the blockchain addresses involved in the transfer. For example, Circle can see every transfer of USDC and the addresses involved, but it knows nothing about either the original or the final owner.
The GENIUS Act and the BSA only regulate the on-ramps and off-ramps — such as exchanges and custodians — where a stablecoin touches the conventional financial system. Between those points, a stablecoin in a self-hosted wallet moves through a pseudonymous layer of a blockchain that no regulator directly controls, and no issuer-focused AML or anti-terrorist finance program reaches.
Aside from stablecoins held in self-hosted wallets, two other routes lead into this pseudonymous layer. The first is to use an offshore exchange that does not care who its customers are or what they do. For example, while UAE-based Binance pleaded guilty to Bank Secrecy Act violations in 2023, its competitors continue to operate outside the United States. The second is to use a mixer such as Tornado Cash, which pools transactions from many users and pays them out in different combinations, severing the link between sender and receiver.
Importantly, these pseudonymous aspects of stablecoins are features, not flaws, of the technology.
The Issuers’ Powers, and Their Limits
Stablecoin issuers do have a potentially powerful enforcement tool that issuers of paper cash lack: they can blacklist blockchain addresses. While a frozen address still holds its tokens, it cannot transfer them. Tether and Circle both maintain such blacklists, and law enforcement can request additions.
Data from AMLBot show how the two issuers use this power. From 2023 through 2025, Tether froze roughly $3.3 billion in USDT across 7,268 addresses. Over the same period, Circle froze roughly $109 million in USDC across 372 addresses — roughly one-thirtieth as much. Yet, rather than suggesting that Tether’s compliance is tougher, the data indicate the predominant path of the illicit flows: namely, on the TRON network, where more than half of frozen USDT sat. According to TRM Labs, TRON hosted more than $26 billion in illicit volumes in 2024, and the UN Office on Drugs and Crime calls USDT on TRON the preferred choice for fraudsters and money launderers in East and Southeast Asia.
Freezing stablecoins can impose losses on illicit users, but it has not been sufficient to close the modified Gresham’s Law gap. To seize the funds, authorities must still identify who controls the frozen blockchain address. But identification occurs only at the points where stablecoins cross into and out of the regulated financial system. This is why analytics firms — such as Chainalysis, TRM Labs, and Elliptic — flag suspect transfers only when they make those crossings. Through no fault of their own, these firms miss peer-to-peer transactions that stay inside the crypto ecosystem and never touch the regulated financial system. The bottom line: for every seizure there is an unknown number of successful illicit transfers.
This brings us back to the trend highlighted in Figure 1: USDT is driving out USDC. Part of that trend likely reflects a network externality: the more people use something, the more useful it becomes to each of them. For stablecoins, this externality means liquidity attracts liquidity. Exchanges in less rigorous regulatory regimes list the coin because their users want it; merchants outside those regimes accept it because exchanges support it. So, the more illicit users adopt a particular coin, the more useful it becomes for other illicit users. In this sense, USDT's dominance is an equilibrium outcome of a market where compliance is costly and pseudonymity has clear, if criminal, benefits.
The Other Side of the Coin?
Stablecoins in self-custody are bearer instruments. The same architecture, however, also serves people not engaged in underlying crimes (such as drug trafficking, human trafficking, or terrorist finance) but who wish to escape surveillance, sanctions, and capital controls.
Consider a Russian family that, after the invasion of Ukraine, wants to send money to a child studying abroad — blocked by capital controls and cut off from banks by sanctions. Or a Venezuelan small-business owner seeking to protect savings from hyperinflation, or an Iranian academic trying to receive payment from a foreign publisher. Stablecoins can serve all of them for the same reason they serve criminals: the transfer is untraceable. The claim moves without asking the sending country, the receiving country, or any well-regulated financial entity in between.
This “dual-use pattern” is an unavoidable consequence of the current technology. Any compliance architecture powerful enough to stop North Korean hackers is also powerful enough to block a dissident’s tuition payment. Conversely, any architecture permissive enough to preserve the dissident’s savings is also permissive enough to allow funding of the Islamic Revolutionary Guard Corps. The current architecture cannot tell them apart.
We already know one potential way out. Duffie, Olowookere, and Veneris describe a "compliance-by-design" architecture that dissociates identity verification from the transaction itself. A regulated identity provider — a bank or similar institution — verifies the user offline and issues a credential. When the user transacts, a cryptographic technique known as a zero-knowledge proof demonstrates that the user holds a valid credential without revealing the user's identity. The transaction settles on the blockchain; the identity records stay with the provider, who monitors suspicious patterns. Using appropriate legal processes, authorities can also compel the provider to identify a credential holder.
Governments and legitimate financial providers alike should welcome innovations that preserve privacy and help expose criminal activity. Unfortunately, this elegant idea is not immediately practical. The reason is that a zero-knowledge proof adds cost to each transaction and slows it down (increasing what experts call latency). That overhead also sits on top of the existing, nontrivial cost of moving stablecoins (see Aldasoro, Frost, and Ito). Reducing all these costs sufficiently to motivate widespread adoption of “compliance by design” likely will remain a challenge for some time.
The potential benefits are sufficiently attractive that international regulators should consider acting now, for example, by sponsoring a cross-border pilot program that offers a regulatory safe harbor for stablecoin issuers adopting compliance-by-design architecture. This sandbox approach would provide for experimentation even before costs fall to the level required for widespread uptake.
The Way Forward: From Issuers to Instruments
Applying the modified Gresham’s Law to stablecoins leads us to expect that USDT will continue to displace USDC. Criminals’ demand is large enough to sustain the market for an anonymous bearer instrument: a coin that no regulator can reach outside the conventional architecture will serve users who want to be unreachable.
The traditional financial system has begun to offer a highly competitive alternative that should help enforce, rather than undermine, the law. As we explored in detail in a prior post, tokenized deposits have compelling advantages over stablecoins for both institutional and retail users. Tokenized deposits are claims on banks that are recorded on digital ledgers. On permissioned ledgers, every holder is an identified customer and every transfer goes through the bank. On other ledgers, the bank can whitelist only those identified clients for whom it can vouch. Either way, the bank verifies the identity of holders from the start.
Tokenized deposits offer the key features stablecoin advocates highlight — programmable transfers, near-instant settlement, 24-hour availability, dollar denomination. Put simply, they are what stablecoins would be if regulation reached the instrument as well as the issuer. For most users, most of the time, a tokenized deposit is what they need. Stablecoins likely will survive, but they may thrive only where anonymity itself is the product. Indeed, as long as the modified Gresham’s Law operates, bad stablecoins will continue to displace good ones.